The Information Security Officer (ISO) is responsible for your company's information security.
Information security is no longer a side issue – not even for SMEs.
Whether filled internally or externally, the role of the ISB is crucial for compliance, resilience and trust. And it should be clearly defined, professionally filled and effectively implemented.

You don't need to build an expert team – we are happy to be your external Data Security Officer.
ISMS by the ISO
Security management by an Information Security Officer (ISO) forms the basis for protecting sensitive information in companies and authorities.
The ISO plays a central role here: it acts as an interface between IT and management and advises both sides on all information security issues. At the same time, it is responsible for establishing and continuously developing appropriate protective measures.
An ISO sets the Information security strategy operational um, based on the goals of the management. However, overall responsibility always remains with the company management.
Overall, the Information Security Officer makes a crucial contribution to the stability, legal certainty, and future viability of a company.
ISO Roles and Responsibilities Overview
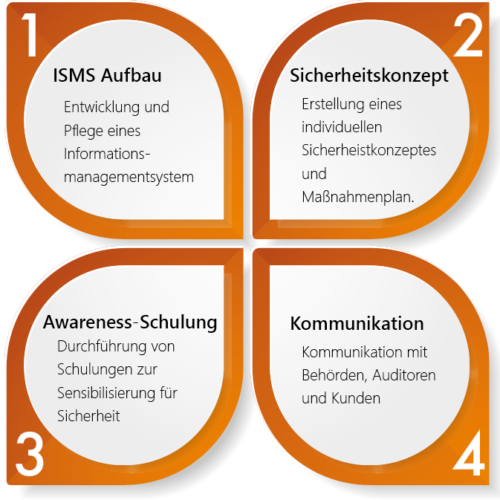
An Information Security Officer (ISO) ensures that company-wide information is effectively protected against threats, vulnerabilities, and system failures. They are responsible for the introduction, implementation, and continuous monitoring of a structured Information Security Management System (ISMS). Their core responsibilities include:
Information security officers manage an information security management system (ISMS) according to recognised standards such as IISO 27001 or TISAX® This involves creating comprehensive policies, procedures, and guidelines that serve as the foundation for effective information security. This is particularly important for structuring organisational processes and clearly defining responsibilities.
Regular reviews and audits of information security measures are essential. The Information Security Officer (ISO) ensures that legal regulations and internal security policies are consistently adhered to. This continuous monitoring helps to identify potential vulnerabilities early and to react in a timely manner. Furthermore, the security strategy often aligns with the recommendations of the BSI (Federal Office for Information Security) to meet the current standards and best practices in the field of IT security.
A key component of the security strategy is the Staff awareness. This covers current threats, risks, and best practices to promote a security culture within the company.
The ISO identifies and assesses security risks that may affect the company. It develops tailored proposals for risk mitigation and implements both technical and organisational measures to improve the security posture.
The identification, assessment, and management of information security risks are of great importance. The Information Security Officer (ISO) places particular emphasis on data confidentiality by proposing appropriate measures to prevent unauthorised access to sensitive information. This includes both technical and organisational measures aimed at ensuring the integrity and confidentiality of company data.
As a consultant to senior management, the external ISO provides valuable insights into all information security matters. It produces detailed reports on the current security status and formulates recommendations to improve security strategies in order to strengthen the company's resilience.
Consultative information security officers actively support companies in preparing for external audits and certifications, such as ISO 27001. He accompanies and coordinates the entire audit process, ensuring all requirements are met.
An important aspect of the security strategy is the development of emergency plans and incident response processes. The ISO provides support in responding to security incidents, whether it's a data breach or a cyber attack, ensuring that the company can act quickly and efficiently.
- main area of responsibility for the information security officer is the Document and Report all safety-relevant processes. This task ensures Transparency, traceability and the continuous improvement of an information security management system (ISMS).
The ISO regularly produces:
Security reportsThese reports document the current state of information security, identified vulnerabilities, audit findings, and the status of ongoing measures. They serve as a basis for management decisions.
Action plansFollowing the risk assessment, the ISO defines specific measures for risk mitigation, prioritises them, and sets deadlines and responsibilities.
Security policies and conceptsThe ISO develops binding rules and regulations, e.g. password policies, access policies or the overarching security concept. These documents form the rulebook for secure behaviour within the company.
Through consistent documentation, the information security officer ensures that File audits, statutory requirements are met and safety objectives are systematically pursued.
Internal or external? When an external Information Security Officer makes sense
In our experience, the internal staffing of the ISO is fundamentally sensible if it possesses the necessary skills and if the required budget is available.
However, many SMEs try to cover the tasks of an information security officer in addition to their duties through IT managers or other specialists. This often leads to Conflict of interest (e.g. checking one's own processes) or. lack of independence or Resource shortages (Time, Staff, Prioritisation, Expertise)
One External Information Security Officer offers an effective alternative here.
Advantages of an external ISO
- Fast availability without lengthy recruiting
- Objectivity and a neutral external perspective
- High Professional qualifications and experience
- Planable, Scalable cost structure
- Clear Methodical approach
- Smooth Collaboration with internal IT and management
Tasks, duties, and role of the ISO
An Information Security Officer ensures clear responsibilities, structured risk management, and legally compliant processes for handling information. They analyse security vulnerabilities, coordinate cross-departmental protection measures, and monitor compliance with internal and external regulations. From implementing effective security policies to training staff, the ISO plays a central role in protecting sensitive data and systems.
The goal: To make information security measurable – through defined KPIs, documented measures, and continuous security assessment within the company.
Another important aspect is risk assessment and management: The ISO conducts regular security assessments and risk analyses to identify potential threats and implement appropriate risk mitigation measures. Furthermore, it is responsible for responding to security incidents and initiating suitable measures in the event of security breaches. This also includes continuous monitoring of security alerts and the implementation of new technologies to improve the security infrastructure.
Duties of an Information Security Officer
Legal requirements and competences of an ISB
Below is an overview of the key legal requirements and the sectors in which the appointment of an Information Security Officer (ISO) may be required.
Businesses that operate critical infrastructures (KRITIS) are subject to IT Security Act obliged to implement information security measures. These companies, which include areas such as Energy, Healthcare, Transport and Finance bear a special responsibility. As a failure of their IT systems would have far-reaching consequences for society, it is mandatory for them to ensure IT security at the highest level.
With the NIS2 Directivee The EU is significantly expanding the security requirements for companies in essential sectors. This directive, aiming to improve the security of network and information systems, requires companies in certain industries to strengthen their IT security. This often includes the necessity to appoint information security officers, who are responsible for implementing and monitoring information security measures. The NIS2 directive affects a wide range of industries, from utilities and transport to communications and healthcare facilities.
Companies that have an Information Security Management System (ISMS) according to ISO 27001 Whether introducing or seeking certification for an Information Security Management System (ISMS), organisations face the task of defining clear responsibilities for information security. While the standard does not explicitly require the appointment of an Information Security Officer (ISO), in practice, it is sensible to entrust a central person with the management and supervision of the ISMS. This person usually takes on a similar role to an information security officer and contributes to ensuring security standards.
In specialised sectors, such as the automotive industry, additional safety requirements apply, which may necessitate the appointment of an ISB. One example of this is the TISAX® standard, which was developed specifically for suppliers in the automotive industry to ensure information security for confidential data along the supply chain. In such cases, an Information Security Officer helps to meet industry-specific security requirements and support certification.
When is the appointment of an information security officer required?
The appointment of an Information Security Officer (ISO) is not legally required for all companies. Nevertheless, various regulatory requirements – for example, under the IT Security Act, the GDPR, or certifications such as ISO 27001 – may make the appointment of an ISO necessary. Industry-specific standards like TISAX® may also require the use of an Information Security Officer.
Operators of critical infrastructures are thus obliged, for example, under the IT Security Act to implement appropriate measures to ensure IT security in certain areas such as energy, water, food, and information technology and telecommunications. In this context, the appointment of an ISB may also be necessary.
Therefore, it is advisable to carefully analyse the individual legal frameworks and the specific requirements of the respective industry. This will not only help to avoid possible legal risks and sanctions but also to improve information security within the company in a targeted and sustainable manner.
Distinction from the Data Protection Officer
Furthermore, the European Union's General Data Protection Regulation (GDPR) requires certain companies to appoint a data protection officer. This person may have similar or overlapping duties to an ISO.
A data protection officer is required if the company's main activities involve the extensive, regular and systematic monitoring of individuals or if special categories of data or data relating to criminal convictions and offences are processed.
Why an ISB is useful even without a legal obligation
Even if there is no explicit legal obligation to appoint an ISO, it can still be beneficial for many organisations, particularly if they process sensitive or personal data.
An ISO helps to minimise the risk of data breaches, ensure compliance with laws and regulations, and thereby avoid potential fines. Furthermore, it strengthens customer trust in the company's security practices.
YOUR CONTACT PERSON
Connect with our expert.
Non-binding, uncomplicated, but always with
added value for you.
RALPH DÖRFLER
Head of IT Security


